Kerberos Single sign-On over SSH under OS X
An advantage of using Kerberos along with SSH is that it makes entering passwords obsolete when establishing connections. Unfortunately this is not working out of the box under OS X in the first place:
1$ kinit cstan@STANKOWIC.LOC
2cstan@STANKOWIC.LOC's password:
3
4$ klist
5Credentials cache: API:xxx
6 Principal: cstan@STANKOWIC.LOC
7
8 Issued Expires Principal
9Oct 22 11:17:30 2016 Oct 22 21:17:37 2016 krbtgt/STANKOWIC.LOC@STANKOWIC.LOC
10
11$ ssh cstan@giertz.stankowic.loc
12cstan@giertz's password:
In spite of having a valid Kerberos ticket it is still necessary to enter a password. The reason for this behavior is that the SSH client is not using GSSAPI (Generic Security Service Application Program Interface). The following command did the trick for my OS X installation:
1$ ssh -o GSSAPIAuthentication=true cstan@giertz.stankowic.loc
According to StackOverflow it might also be necessary to specify the GSSAPITrustDNS parameter.
The avoid specifying these options with every single SSH command, they can be stored in configuration files - e.g. in your personal SSH configuration ˜/.ssh/config:
1GSSAPIAuthentication yes
2
3Host *
4 User cstan
The last two lines ensure to pre-select a username for all SSH connections. As a result, you also don't need to enter a username. 🙂
Of course you can override this behavior by specifying a different username with the -l parameter. It is also possible to override these settings per hostname or domain:
1Host *
2 User max
3
4Host *.mydmz.loc
5 User simone
SSH logins should now be possible without specifying a username and password as long as a valid Kerberos ticket is available:
1$ ssh giertz
2Last login: Sat Oct 22 11:38:13 2016 from shittyrobots.loc
3
4$ whoami
5cstan
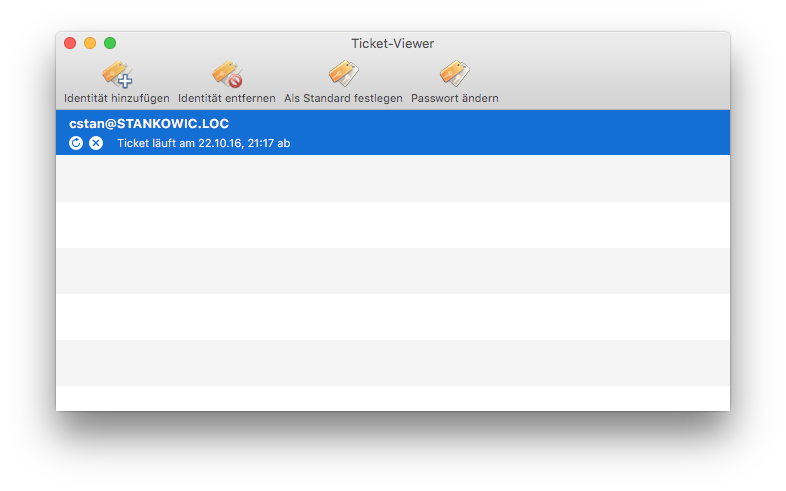
OS X also offers a hidden ticket viewer as an alternative for using kinit to generate tickets. The tool can be found at /System/Library/CoreServices/Ticket-Viewer.app, it is a frontend for the Kerberos utilities: