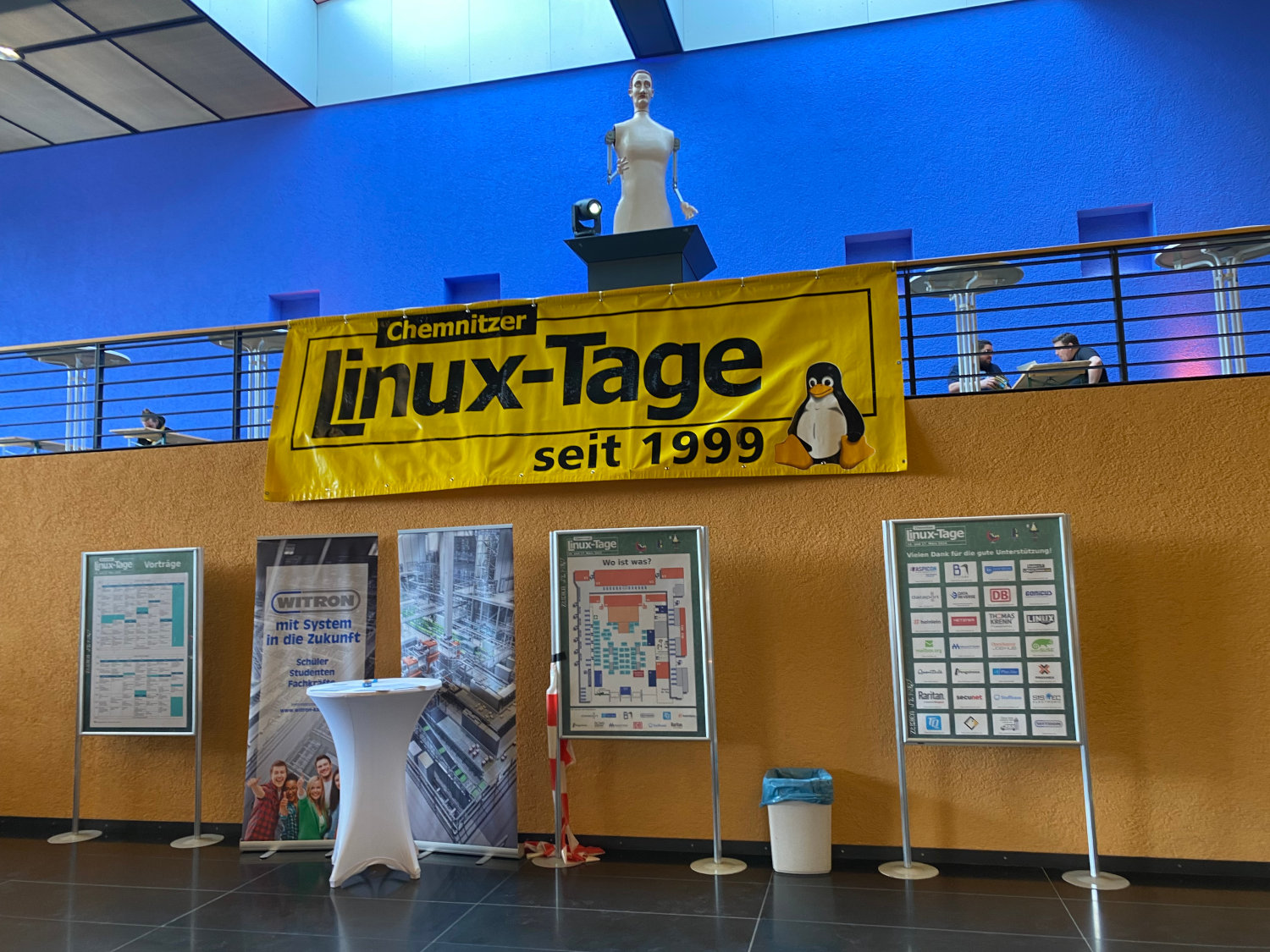
Chemnitzer Linux Tage 2024

Last weekend, the 19th Chemnitz Linux Days took place at Chemnitz University of Technology under the motto "Setting an example". The conference is one of the oldest and largest Linux and open source events in the German-speaking world. For me it was an absolute novelty, the distance had always put me off. There were 3200 participants on site and 300 viewers for the live streams.
Talks and workshops
As usual, the program was extensive and consisted of a total of 94 talks, 10 workshops and 8 courses for children. The content quality of the talks was generally very high and exceeded what I was used to from other conferences. The recordings were available on media.ccc.de within a short time.
In one of the first presentations Warum sich IT-Security erneuern muss, Patrick Münch described the desolate state of IT security in companies and public authorities and presented Mondoo, a toolkit that can help improve it. In addition to a dashboard offering, the open source tools cnspec and cnquery were also demonstrated, with which infrastructure (VMs, container images, Kubernetes, etc.) can be examined and interactively analyzed for security vulnerabilities.
In his presentation Ransomware-Angriffe abwehren mit Linux und Open Source , Klaus Knopper showed various attack scenarios and applications to prevent them. He also uncovered myths surrounding data loss and named tools for recovering data.
In the presentation Einführung in Mail-Verschlüsselung für Rookies, Andreas Grupp explained mail encryption using the S/MIME and GnuPG standards as examples.
I also found the presentation SSH-Login mit FIDO-Tokens statt Keyfiles by Jirka Kraml interesting, in which he explained FIDO2 and the various associated key types. He also demonstrated how to secure SSH logins with a Yubikey.
The omnipresent topic of Proxmox was also discussed at the conference. In his presentation Of Heroes & Hypervisors: Proxmox VE & Proxmox Backup Server, Jonas Sterr showed various installation scenarios - from individual systems and cluster setups to the hyperconverged approach. He also explained the Ceph principle and the purposes of Proxmox Backup Server.
SAML 2.0 and OIDC 1.0 were discussed in Silke Meyer's presentation Single Sign-on für Web-Anwendungen. Here the basic differences between LDAP and IdP were explained using the example of Keycloak and Shibboleth.
I followed the talk VirtualBox Meets KVM by Julian Stecklina with great interest. In this talk, a development was presented that makes it possible to use Oracle VirtualBox with a KVM backend. Usually, a proprietary Oracle development is used here, which is less performant and also requires manual effort, especially in connection with Secure Boot. Experimental builds are currently available that have to be compiled manually - the functionality was demonstrated live.
In his presentation Sichere Datenhaltung und Backup in der Cloud, Stefan Schumacher compared the gocryptfs and cryfs file systems, which are suitable for secure backups in cloud storage. He also presented the tools duplicity and rclone.
In the presentation Dokumentation als Code mit Ansible und Asciidoctor, Christoph Stoettner demonstrated an automated documentation process for Ansible code using Asciidoctor. In addition to the creation of corporate identity templates, various toolkits for appealing graphs were also outlined. The basics of Asciidoctor were also explained.
In her talk Administration und Moderation auf Mastodon, Stephanie Henkel reported on her experiences with the moderation and administration of the Mastodon instance dresden.network. In addition to some Fediverse basics, the principles of geoblocking and federation were also covered.
I found the presentation Was ist eigentlich Bareos? by Andreas Rogge no less interesting. He gave an insight into the backup software Bareos, which I had heard about several times but never looked at in depth. In addition to the current status, further developments were also touched on. I will take a closer look at the software afterwards.
vim enthusiasts were able to improve their skills in the workshop vim Basisworkshop: mit wenig Zeichen viel erreichen, while those interested were able to get into the development of Linux drivers in the Linux Treiber Workshop.

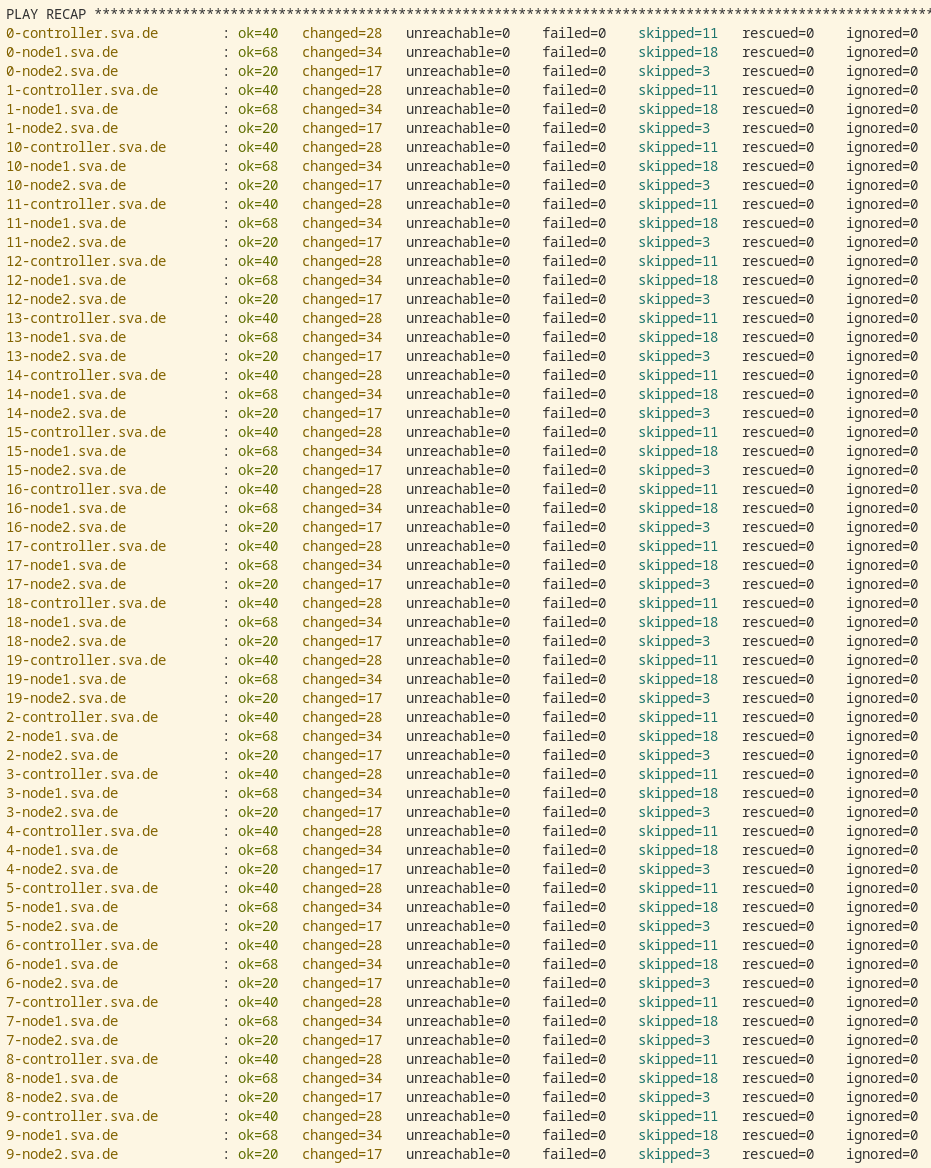
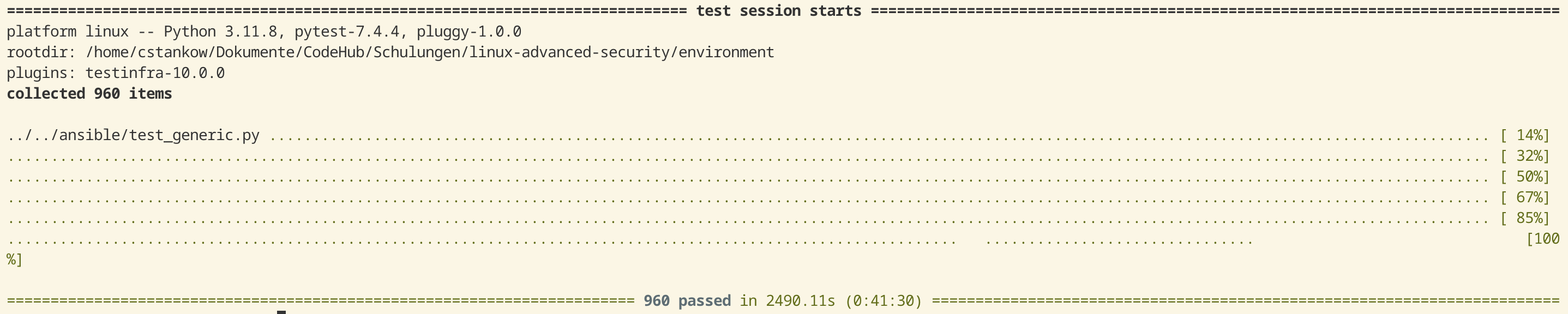
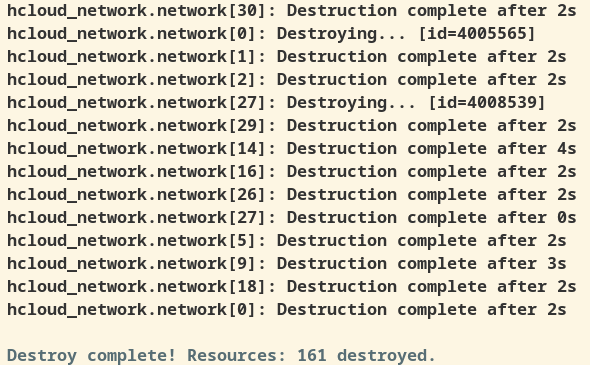
I myself was also able to contribute to the workshop program with Linux Security-Grundlagen. The session showed various ways and means of hardening Linux systems both manually and automatically. Unexpectedly, the workshop was fully booked with 30 participants - which meant that the prepared learning environment had to be adapted again at short notice. I usually design training courses to be as interactive as possible: with a few slides and lots of practical tasks to directly apply what I have seen. For these tasks, I provide virtual machines in a cloud environment that the participants can then use. To ensure that all systems are in the desired state, I run pytest unit tests. In this case, almost 100 VMs had to be checked with approx. 1300 unit tests - which took a whopping 80 minutes. One learning from this was to use pytest-xdist to parallelize these tests on different CPU cores and thus significantly reduce the waiting time. I never held a workshop with so many participants and was very positively surprised at how well the infrastructure performed.
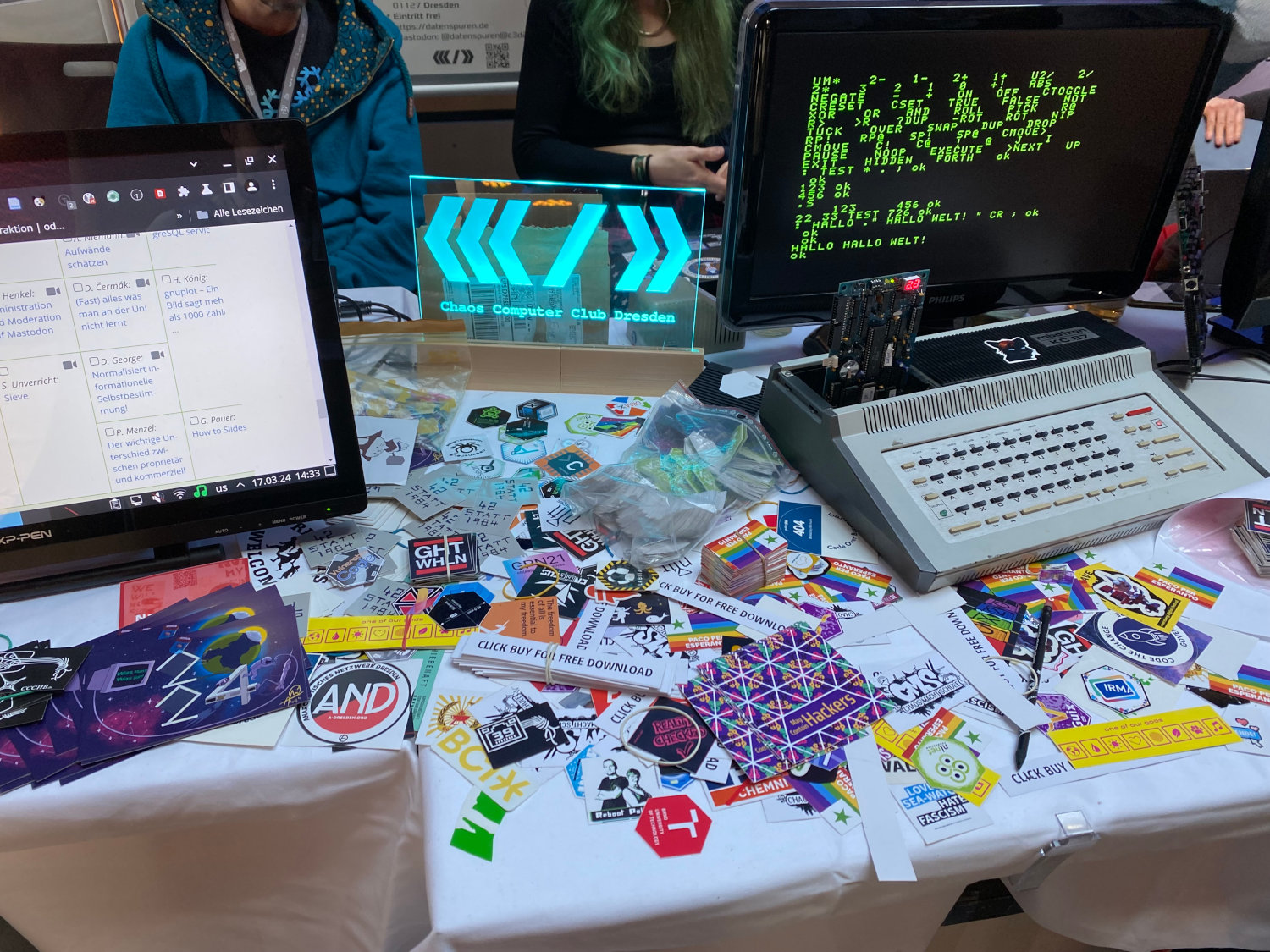
Booths
Another added value was the exchange of experiences at the numerous stands.


I was able to have a very nice and informative conversation with Hetzner and find out more about the Bareos software at the stand of the same name.
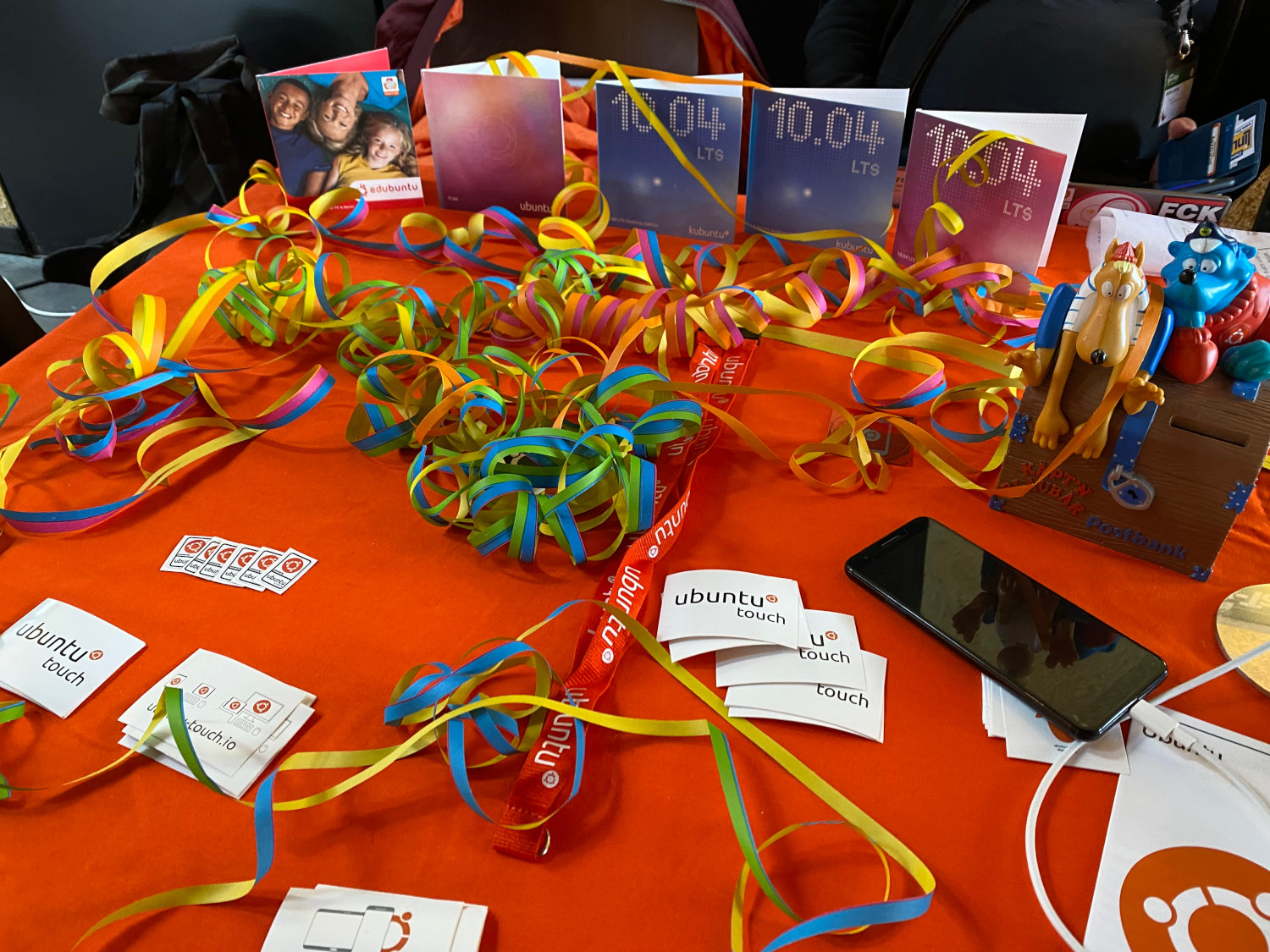
At the Ubuntu stand, the celebrations for the 20th anniversary in October of this year were already underway. In addition to almost forgotten installation media, there was also the opportunity to exchange old anecdotes.


TUXEDO Computers demonstrated current devices, while various open source projects (Ansible, NixOS, RIOS-OS, etc.) showed their current developments and offered help with problem solutions.
At the booths of Thomas Krenn and Heinlein Support I was able to exchange experiences regarding Proxmox. So now I finally know a solution to my recent OCFS2 problem.
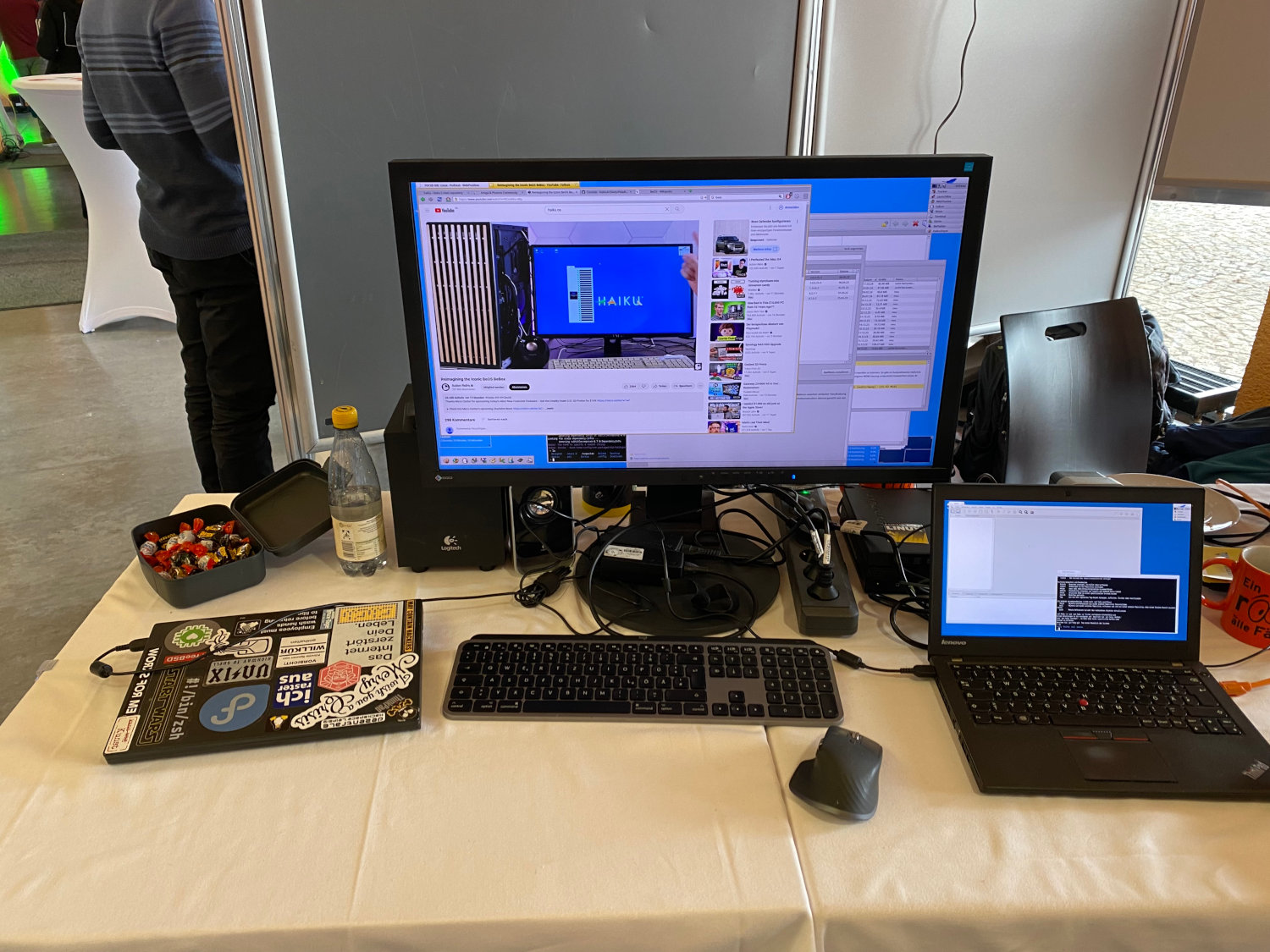
I visited the Haiku project's booth with great interest. I have been experimenting with the open source operating system, which is binary-compatible with BeOS, on and off for over 10 years. It is remarkable that the project has been under development for over 20 years and is therefore by no means old retro iron. I was able to talk to two users of the project for a long time and had a lot of fun.
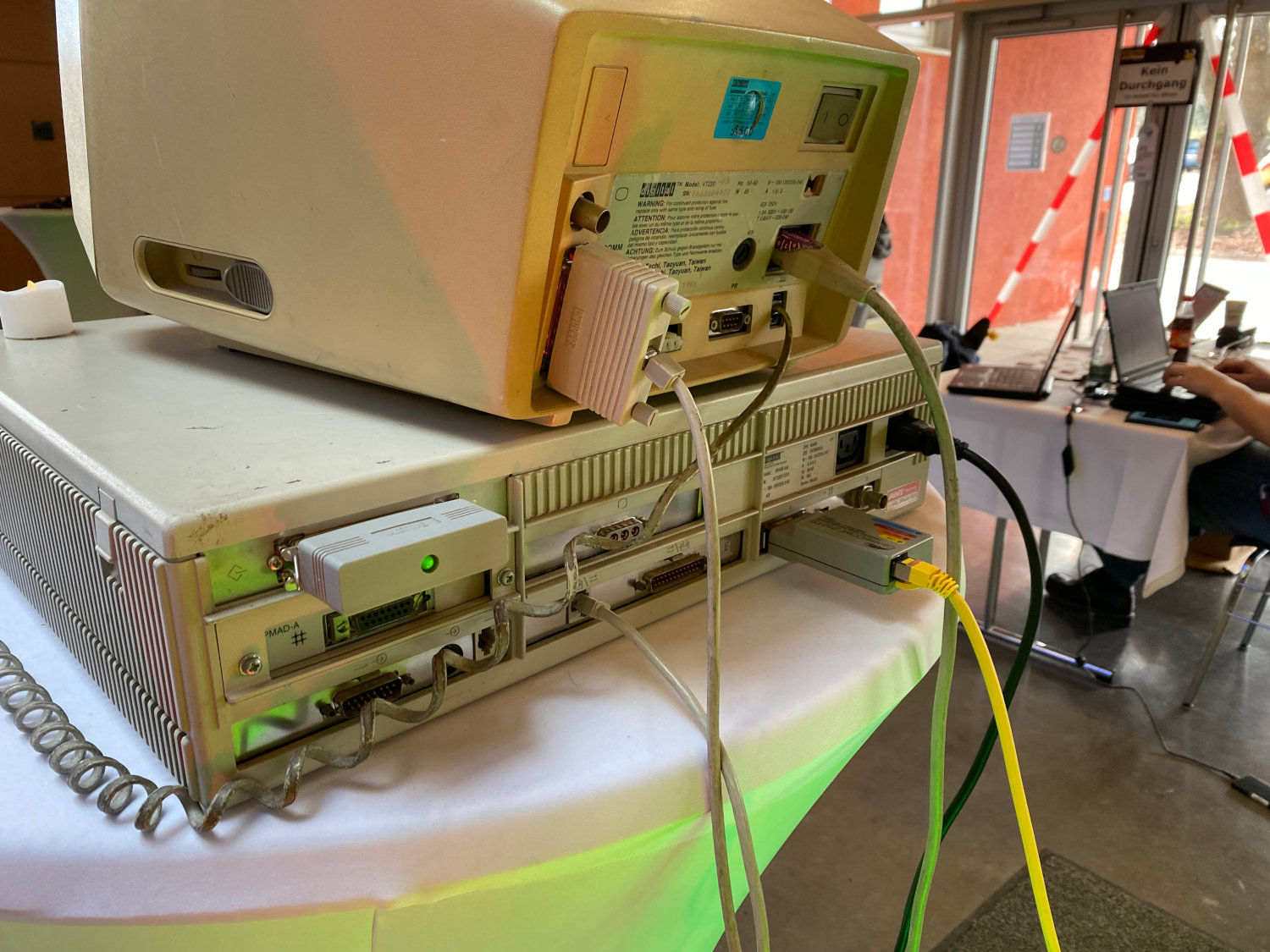
The DEC VAXstation 4000 90 exhibited by illumos and OpenIndiana was very eye-catching. The over 30-year-old workstation clocks at just under 75 MHz and was equipped with 128 MB RAM. Of course, NetBSD was installed as the operating system. A SCSI hard disk and network access were added to the device. The connected VT220 terminal is over 40 years old and still works perfectly.


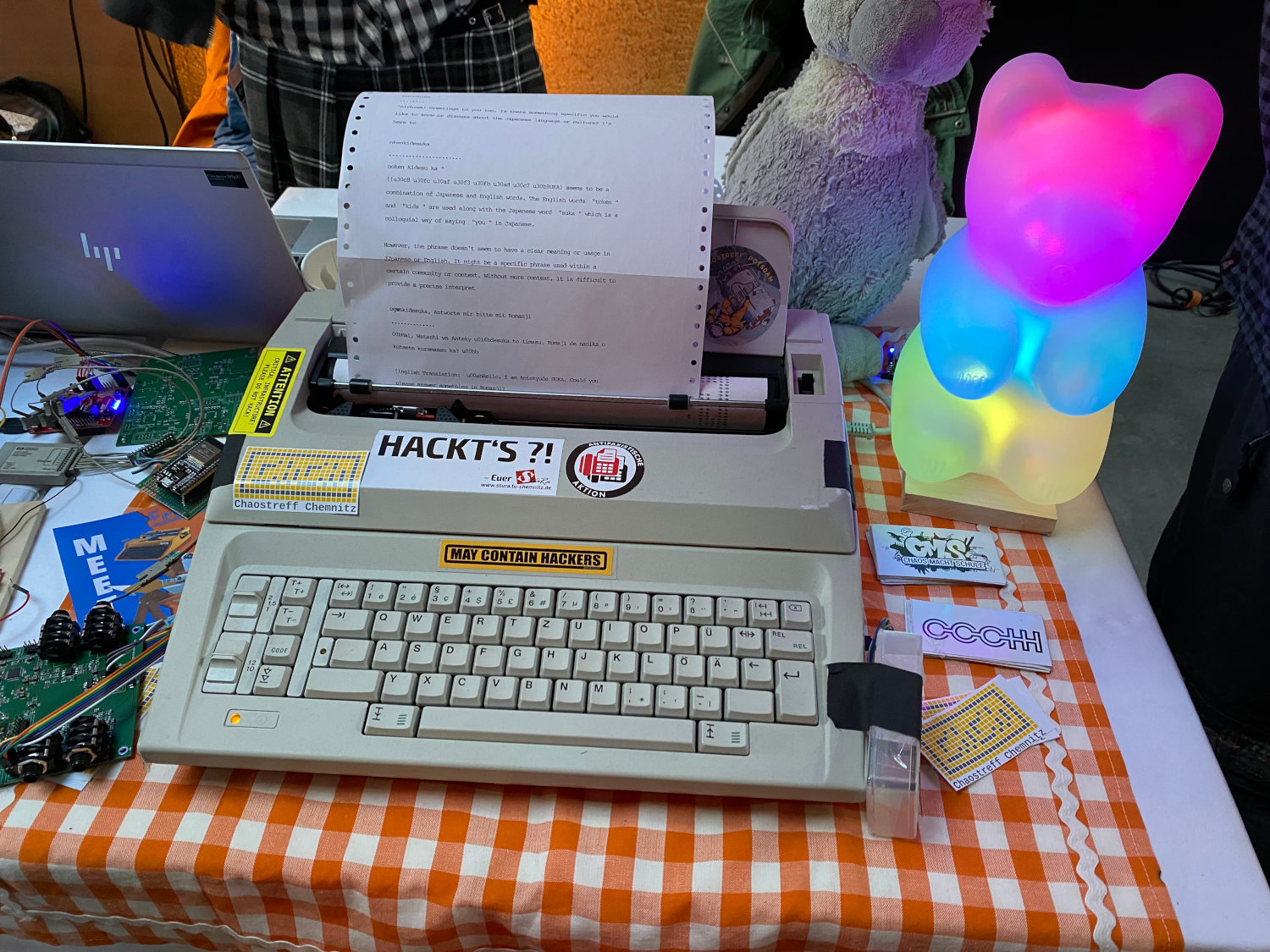
The stands of regional hackspaces, such as the ChaosTreff Chemnitz, were also interesting. Here the Erika typewriter could be examined and tried out. This is a typewriter from VEB Robotron, which - equipped with an ESP32 - was enabled to interact with ChatGPT. Karola Köpferl explained the background to this in the presentation Erika setzt jetzt selber Zeichen.
Further offer
A social Event took place on Saturday evening, which was used for networking and exchanging experiences. After pre-registration, LPI exams could be taken at fair prices and in the Praxis Dr. Tux devices brought along could be repaired by volunteers.
Conclusion
I was very positively impressed by the conference! The organization and communication beforehand was extremely professional and everything went as expected on site. There were lots of helping hands, I have absolutely nothing to complain about. I would love to come back next year. 🙂
Daniel Schreiber and Philipp Skotnik gave an insight into the organization of the conference in their presentation make CLT. Also worth mentioning is the summarizing blog article of the CLT.